- Main
- Computers - Networking
- Practical reverse engineering: x86,...

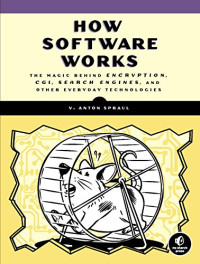
Practical reverse engineering: x86, x64, ARM, Windows Kernel, reversing tools, and obfuscation
Bruce Dang, Alexandre Gazet, Elias Bachaalany, Sébastien Josse你有多喜欢这本书?
下载文件的质量如何?
下载该书,以评价其质量
下载文件的质量如何?
Analyzing how hacks are done, so as to stop them in the future
Reverse engineering is the process of analyzing hardware or software and understanding it, without having access to the source code or design documents. Hackers are able to reverse engineer systems and exploit what they find with scary results. Now the good guys can use the same tools to thwart these threats. Practical Reverse Engineering goes under the hood of reverse engineering for security analysts, security engineers, and system programmers, so they can learn how to use these same processes to stop hackers in their tracks.
The book covers x86, x64, and ARM (the first book to cover all three); Windows kernel-mode code rootkits and drivers; virtual machine protection techniques; and much more. Best of all, it offers a systematic approach to the material, with plenty of hands-on exercises and real-world examples.
• Offers a systematic approach to understanding reverse engineering, with hands-on exercises and real-world examples
• Covers x86, x64, and advanced RISC machine (ARM) architectures as well as deobfuscation and virtual machine protection techniques
• Provides special coverage of Windows kernel-mode code (rootkits/drivers), a topic not often covered elsewhere, and explains how to analyze drivers step by step
• Demystifies topics that have a steep learning curve
• Includes a bonus chapter on reverse engineering tools
Practical Reverse Engineering: Using x86, x64, ARM, Windows Kernel, and Reversing Tools provides crucial, up-to-date guidance for a broad range of IT professionals.
Reverse engineering is the process of analyzing hardware or software and understanding it, without having access to the source code or design documents. Hackers are able to reverse engineer systems and exploit what they find with scary results. Now the good guys can use the same tools to thwart these threats. Practical Reverse Engineering goes under the hood of reverse engineering for security analysts, security engineers, and system programmers, so they can learn how to use these same processes to stop hackers in their tracks.
The book covers x86, x64, and ARM (the first book to cover all three); Windows kernel-mode code rootkits and drivers; virtual machine protection techniques; and much more. Best of all, it offers a systematic approach to the material, with plenty of hands-on exercises and real-world examples.
• Offers a systematic approach to understanding reverse engineering, with hands-on exercises and real-world examples
• Covers x86, x64, and advanced RISC machine (ARM) architectures as well as deobfuscation and virtual machine protection techniques
• Provides special coverage of Windows kernel-mode code (rootkits/drivers), a topic not often covered elsewhere, and explains how to analyze drivers step by step
• Demystifies topics that have a steep learning curve
• Includes a bonus chapter on reverse engineering tools
Practical Reverse Engineering: Using x86, x64, ARM, Windows Kernel, and Reversing Tools provides crucial, up-to-date guidance for a broad range of IT professionals.
年:
2014
出版:
1
出版社:
Wiley
语言:
english
页:
384
ISBN 10:
1118787315
ISBN 13:
9781118787311
文件:
PDF, 4.57 MB
您的标签:
IPFS:
CID , CID Blake2b
english, 2014
在1-5分钟内,文件将被发送到您的电子邮件。
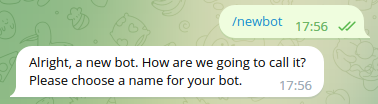
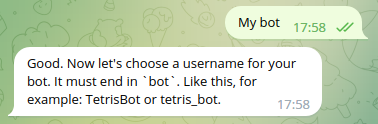
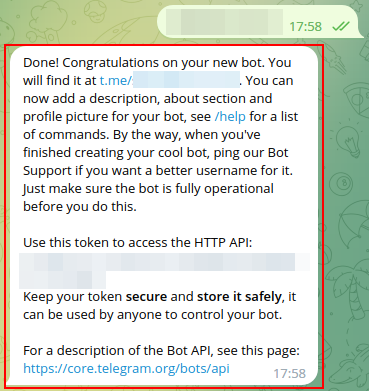
该文件将通过电报信使发送给您。 您最多可能需要 1-5 分钟才能收到它。
注意:确保您已将您的帐户链接到 Z-Library Telegram 机器人。
该文件将发送到您的 Kindle 帐户。 您最多可能需要 1-5 分钟才能收到它。
请注意:您需要验证要发送到Kindle的每本书。检查您的邮箱中是否有来自亚马逊Kindle的验证电子邮件。
正在转换
转换为 失败
关键词
关联书单















































































































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org  转换文件
转换文件 更多搜索结果
更多搜索结果 其他特权
其他特权